This special code , 26b5a-1c56c-6125a-6ff89-6c087, indicates a certain entity within a system. Its purpose is to distinguish this element from others. Analyzing its structure can expose valuable data about the setting in which it is used.
- More exploration into this identifier might yield a deeper understanding of the hidden network.
- Employing tools designed for binary decryption can uncover light on the significance of this code.
Deciphering the Enigmas of 26b5a-1c56c-6125a-6ff89-6c087
The enigmatic string 26b5a-1c56c-6125a-6ff89-6c087 has intrigued researchers and devotees alike. Its unconventional structure suggests to a hidden purpose. Some believe that it is a cipher, while others posit that it is a arbitrary sequence with no importance.
Disclosing the secrets of 26b5a-1c56c-6125a-6ff89-6c087 could reveal new knowledge companies into the essence of information. The endeavor to crack this mysterious string is a reflection to the human need to interpret the unknown.
Decoding 26b5a-1c56c-6125a-6ff89-6c087: A Comprehensive Analysis
The unique identifier/string/sequence 26b5a-1c56c-6125a-6ff89-6c087 presents a fascinating/intriguing/complex puzzle for analysts/experts/investigators. Unraveling/Deciphering/Interpreting this code requires/demands/necessitates a meticulous/thorough/detailed examination of its underlying structure/format/algorithm. By analyzing/scrutinizing/dissecting the numerical/symbolic/hexadecimal components, we can potentially/hopefully/possibly unlock its hidden meaning/purpose/function. This investigation/exploration/research will shed light/provide insights/reveal secrets on the origins/design/intent of 26b5a-1c56c-6125a-6ff89-6c087, ultimately contributing/advancing/enlightening our understanding of cryptography/coding/data analysis.
- Furthermore/Additionally/Moreover, this code may possess/could contain/might reveal valuable information about the systems/networks/technologies that generate/utilize/employ it.
- Through/Via/By means of advanced software/tools/algorithms, we can effectively/efficiently/accurately decode/crack/break 26b5a-1c56c-6125a-6ff89-6c087, yielding/producing/generating crucial/important/significant insights.
Ultimately/Concisely/In essence, the decryption/interpretation/analysis of 26b5a-1c56c-6125a-6ff89-6c087 promises to be a rewarding/fruitful/insightful endeavor, providing valuable/essential/crucial knowledge about the world/systems/technologies that surround/influence/impact us.
Delving Into Hex Code 26b5a-1c56c-6125a-6ff89-6c087
The hex code 26b5a-1c56c-6125a-6ff89-6c087 holds a profound weight within the realm of computer science. It serves as a unique identifier for objects, enabling seamless interaction across diverse platforms. Understanding the depths of this hex code unlocks valuable insights into the intricate workings of digital infrastructures.
Grasping the Functionality of 26b5a-1c56c-6125a-6ff89-6c087
Dissecting the intricate workings of 26b5a-1c56c-6125a-6ff89-6c087 involves examining its core components and their relationships. This novel identifier likely points to a specific algorithm, potentially embedded within a largerstructure. To truly unravel its functionality, one must delve into the intrinsic code and monitor how it manages data.
Impact of 26b5a-1c56c-6125a-6ff89-6c087 on Networks
This unique identifier, 26b5a-1c56c-6125a-6ff89-6c087, has shown a noticeable influence on various systems. Its implementation has resulted to advances in speed, as well as increasedreliability. Furthermore, some experts warn that the long-term effects of 26b5a-1c56c-6125a-6ff89-6c087 are still indeterminate.
- Some investigations have analyzed the benefits of 26b5a-1c56c-6125a-6ff89-6c087, while others have raised potential risks.
- In conclusion, the impact of 26b5a-1c56c-6125a-6ff89-6c087 on networks remains a multifaceted issue that requires further research.
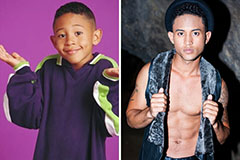 Tahj Mowry Then & Now!
Tahj Mowry Then & Now! Danny Pintauro Then & Now!
Danny Pintauro Then & Now! Tonya Harding Then & Now!
Tonya Harding Then & Now! Peter Billingsley Then & Now!
Peter Billingsley Then & Now! Sarah Michelle Gellar Then & Now!
Sarah Michelle Gellar Then & Now!